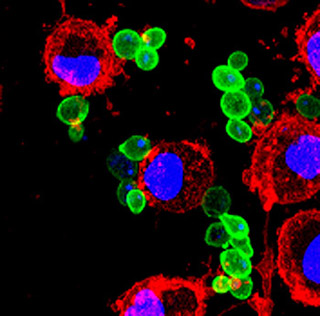
Saccharomyces cerevisiae yeasts (green) in process of being endocytosed and destroyed by dendritic cells (plasma membrane in red, nucleus in blue). (Photomicrograph courtesy of Dr. Eduardo Guillen and Jianzhu Chen. Used with permission.)
Instructor(s)
Dr. Dina Gould Halme
MIT Course Number
7.340
As Taught In
Spring 2004
Level
Undergraduate
Course Description
Course Features
Course Highlights
A full bibliography is included in the readings section of this course.
This course is one of many Advanced Undergraduate Seminars offered by the Biology Department at MIT. These seminars are tailored for students with an interest in using primary research literature to discuss and learn about current biological research in a highly interactive setting. Many instructors of the Advanced Undergraduate Seminars are postdoctoral scientists with a strong interest in teaching. The instructor for this course, Dr. Halme, is a member of the HHMI Education Group.
Course Description
Every infection consists of a battle between the invading pathogen and the resisting host. To be successful, a pathogen must escape the many defenses of the host immune system until it can replicate and spread to another host. A pathogen must prevent one of three stages of immune function: detection, activation, or effector function. Examples of disease-specific immune evasion and the mechanisms used by pathogens to prevail over their hosts' immune systems are discussed. Also considered is what these host-pathogen interactions reveal about the normal function of the immune system and basic cell biological processes, such as protein maturation and degradation.


